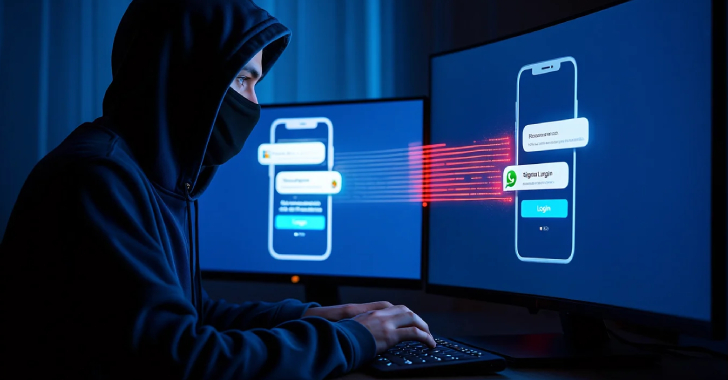
Android Spyware Disguised as Alpine Quest App Targets Russian Military Devices
Cybersecurity researchers have revealed that Russian military personnel are the target of a new malicious campaign that distributes Android spyware […]
Android Spyware Disguised as Alpine Quest App Targets Russian Military Devices Read More »